VMSA-2020-0015 – Critical Severity
Today I have woken to an email from VMware notifying me of some newly discovered critical (9.3) vulnerabilities, these affect a range of products including ESXi 6.5 up to 7. You can find the full list here VMSA-2020-0015
There are a variety of exploits so please check the above link to confirm how your environment is impacted. They include, VMs with 3D Graphics enabled that can allow an attacker to run malicious code on the underlying hypervisor or crash services leading to a partial DOS among others.
Fortunately, there is a fix and a workaround for ESXi which I will cover here.
Workaround: In PowerCLI run the following command to list all VMs affected Get-VM | Get-AdvancedSetting -Name "mks.enable3d"| Select Entity, Name, Value
Once you have your list you can simply disable the parameter:Get-VM VM-Name | New-AdvancedSetting -Name "mks.enable3d" -value $false
Fix: Apply the below patches
ESXi_7.0.0-1.20.16321839
ESXi670-202004101-SG
ESXi650-202005401-SG
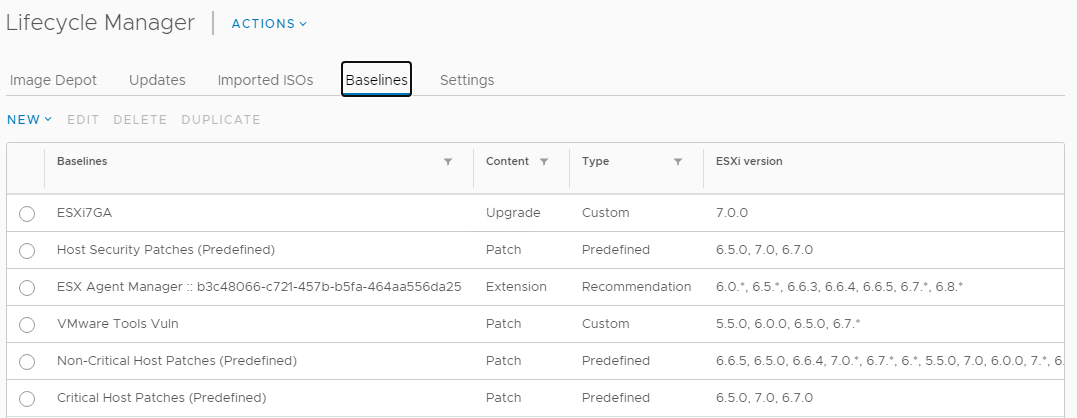
You can do this via Lifecycle Manager (Update Manager) in Center, you should find the patches in the default (Critical Host Patches (Predefined)) baseline or you will need to add them to your custom baselines and patch ASAP.
If you arent already on the mailing list to receive these alerts, i highly recommend you get yourself on there at the following link:
https://www.vmware.com/security/advisories.html
![]()